Microsoft the first to support FIDO2 security key
Published on The Verge | By
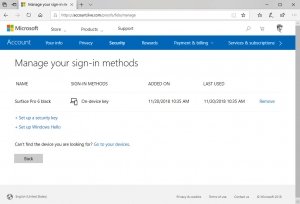
Microsoft is making it easier and more secure to sign into a Microsoft Account today. The software giant is now supporting standards-based FIDO2 security key devices to allow anyone to sign into their Microsoft Account without a username or password. Microsoft is enabling the security key or Windows Hello support through its Edge browser, and it’s the first company to support password-less authentication using the FIDO2 WebAuthn and CTAP2 standards.
If you have the latest Windows 10 October 2018 Update, you’ll be able to set up Windows Hello or a physical security key from Yubico or FEITIAN that support the FIDO2 standard. If you have a device with a Windows Hello webcam or fingerprint reader, you can simply visit Microsoft Account settings with Edge and link a Windows 10 machine to your account so it no longer requires password entry.
This will place a private key on the trusted platform module (TPM) in a Windows 10 device which is used alongside the presence of the physical key or biometric Windows Hello authentication to verify it against the public key stored on Microsoft’s servers. This combination should make it difficult to fall for a phishing scam or malware, as you’ll get used to logging in without credentials or passwords.
Microsoft first enabled its account users to sign in without a password using the company’s iOS and Android Microsoft Authenticator app. It was the first step towards password-less logins, and support FIDO2 security keys is the next logical step. Google and Facebook have already been using USB tokens to secure accounts, and Microsoft is planning to bring this same support to work and school accounts that use Azure Active Directory. As Microsoft has adopted open standards by the W3C and FIDO Alliance standards bodies, Chrome and Firefox will also be able to use these security keys to log into a Microsoft Account once they support the FIDO2 standards.
If you’d like assistance to enable this functionality, give us a call.