You have security, use it to protect your data
By Louis Koen, Managing Member of Crimson Line on 26 July 2019
Cybersecurity Insiders considered information from various resources and found that South African companies are most vulnerable to cyber-attacks. And like many people world-wide, SA business owners think it won’t happen to their company. We’re so used to being targeted for our physical goods – our cellphones, cars, TVs – that you’ll struggle to find anyone who doesn’t have insurance and/or private security. I’d like to suggest that we need to get this serious about our data protection.
Luckily there is a relatively simple way to eliminate around 90% of online threats your business encounter. And you’re already paying for it if you’re using Office 365! It’s called multi-factor authentication (MFA). 90% of cyber-attacks result from a compromised password and if properly configured, MFA will limit the threat of a data breach.
According to Brad Anderson, Microsoft CVP Enterprise Mobility and Management, Microsoft has found that 100 million identities are attacked every month. And given that 50,000 corporate identifies are compromised monthly, it would be foolish to assume that your business isn’t a target and that you’re not likely to be attacked – because you are according to the research by Cybersecurity Insiders.
What is MFA?
“For those that don’t know what MFA is, here’s the background info for context:
Passwords have proliferated across our online lives – they’re required for every single website and web application you use. As you know, this can be quite the headache – no enjoys clicking the ‘forgotten password’ link and having to reset it for the umpteenth time. Historically, we used the same old trusty password for everything (and 59 % of people still do (2)). Then we realized how insecure passwords were and the more diligent of us moved to multiple passwords of higher complexity.
However, no matter how complicated your passwords are, there is always the threat of a brute force or spray attack cracking your password, a phishing email catching you out, or a data breach involving a company your details are registered with. Before you know it, your details could be for sale on the dark web. Want to see if your email addresses have ever been compromised? Check here at https://www.haveibeenpwned.com/ – it takes just a few seconds. You can also take this quiz from Google to see if you can spot a phishing email.
This is where MFA comes in. MFA allows you to add a second form of identity verification to your accounts in addition to your password – your password is the thing you know. The second form of identification must be something unique that you have (e.g. your phone or a FIDO2 security key) or something that you are (e.g. a biometric such as your fingerprint). These are common secondary verification factors. This means that even if your password details fall into the hands of an attacker, they can’t get into your accounts without something unique to you like your mobile phone or fingerprint. These are not easy to get hold of for anyone, let alone a hacker who’s in Russia or China.
Typically, an average MFA system will generate a unique code each time you attempt to login – with the code being associated with your account. For example, you would enter your password and then you would be prompted to enter a code that will be sent to your phone via an SMS text or an email.
However, SMS MFA is not something your business should rely on. While it’s better than leaving MFA turned off, hackers can intercept SMS messages with relative ease – due to an ageing global phone-routing-system and the possibility of SIM Swap attacks.
MFA for Office 365
If your company uses Office 365, it is critical that you implement MFA – which is included in all plans. Office 365 accounts are extremely common targets for hackers; it doesn’t matter if you work for a small business or a global corporation, hackers will randomly attack accounts just because they are using Office 365. If configured with MFA, most of these attacks are unlikely to amount to anything.
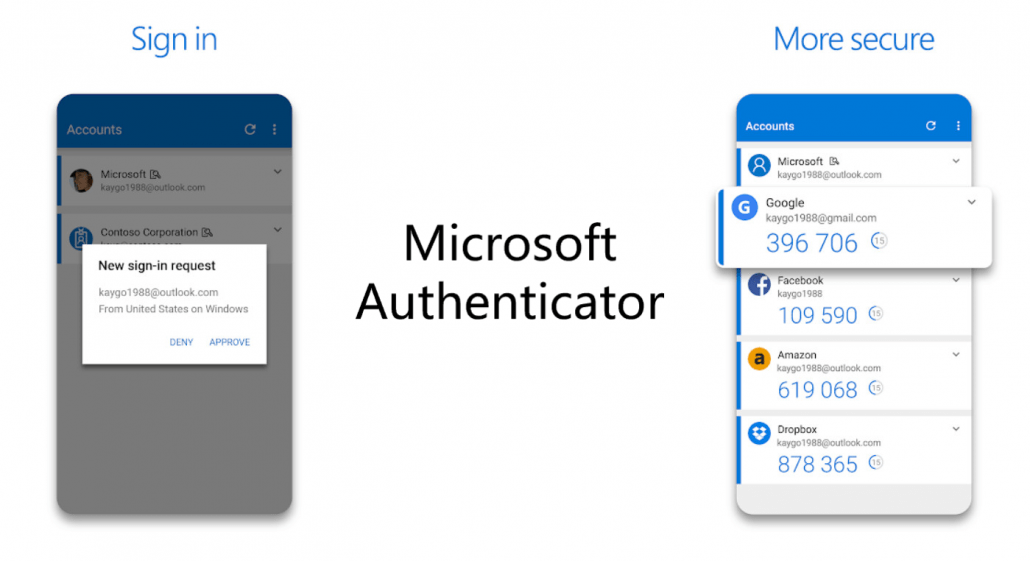
To use MFA with Office 365, the easiest and quickest method requires the installation of the Microsoft Authenticator app on a mobile device. This can be an employee’s work or personal device; it just must be the device which they will always have with them when logging into their Office 365 account.” (1)
How do employees respond to being asked to install a work-related application on their personal phone?
The way the request is made, plays a big role around the reaction employees have. If employees are given company laptops or have access to company email on their personal devices, employees know that it gives them flexibility to work from anywhere. These employees usually are happy to oblige.
Employees who mostly do work when office-bound, usually give a little push back with the request. Therefore, it’s crucial to explain to them the negative effect a data breach can have on confidential client data and company funds as well as reputation. The breach in security will have a direct impact on them, their colleagues, suppliers and clients. One breach could result in a hacker getting the keys to the kingdom. They need to understand that IT security is no longer just the IT department’s responsibility. It’s every employee’s responsibility.
What can users expect when MFA is installed?
On Android, Microsoft Authenticator only takes up 27.38MB once installed. It can be downloaded from Google Play or the Apple Store. When you log in to Office 365 with your account password, you’ll get a prompt on your phone from the Authenticator that you need to approve the log in. That’s it. You can even say it shouldn’t ask you again in the next 14 days. So, it’s not a singular event occurrence. It’s minimal effort with big security protection benefits.
What’s the alternative if employees simply refuse to install MFA?
The company will have to buy an Azure AD Premium P1 license (as a minimum). This will give you the option of adding trusted IPs to your MFA. Your office IP would then be a trusted IP and office-bound employees won’t need to respond to prompts from the Authenticator while at the office. Anyone working outside of the office IP range, will still have to accept prompts.
Beware of legacy protocols
Although setting up MFA in Office 365 is a big win for security at your company, a few security vulnerabilities will, unfortunately, remain. The Authenticator will not prompt users where legacy protocols exist which aren’t compatible with MFA. These include:
- Older Office clients that do not use modern authentication
- Clients that use mail protocols such as IMAP/SMTP/POP
There are cyberattacks that specifically focus on legacy authentication protocols. And MFA won’t protect against this.
However, using an Azure AD Premium P1 license (or a more comprehensive Microsoft security offering such as Enterprise Mobility + Security) will. Azure AD Premium P1 includes the option of using conditional access. Conditional access allows you to block legacy authentication from users, essentially plugging those remaining gaps in your security where MFA isn’t available.
It’s important, so let me say it again, you need to block legacy protocols. Businesses of all sizes are being attacked again and again. Clients who take their security seriously are well-equipped to deal with an attack and for them, business continues as usual.
Just do it!
If you have Office 365, you have MFA. Roll it out, today – after getting buy-in from employees. You’re already paying for it and knowing that it’ll protect you against 90% of attacks, means you’ll be decreasing your security risk considerably. Here’s a guide to do it.
Secondly, depending on your budget, you must get Enterprise Mobility + Security or Azure AD Premium P1 to protect you against the threats of legacy protocols.
The first line of defense in cybersecurity is protecting employees against phishing attacks with Advanced Threat Protection (ATP). In short, it gives you two-fold security – insurance and private security to use my previous analogy. But, more about ATP in my next article.
Not 100% sure how to go about this?
Technology is evolving at an incredible pace. No one person can keep up with everything and security is particularly challenging. As a Microsoft Gold Partner, Crimson Line, has a team of experts who can assist you. We’re happy to share our knowledge and experience gained from continuous training and experience with well-known South African brands. Don’t hesitate to contact one of our friendly solution specialists.